A colossal database, containing over 149 million combinations of usernames and passwords, has been exposed online, accessible to anyone with a simple internet connection and a web browser.
The database, now removed, represented a gold mine for any malicious actor, including credentials for technology giants such as Google and Facebook, cryptocurrency platforms such as Binance, and even access to international government portals.
The discovery sheds new light on the pervasiveness of infostealers and the urgent need for users worldwide to review their personal security measures.
The discovery of an ever-expanding archive

The credit for the discovery goes to Jeremiah Fowler, a security analyst with long-standing experience, who stumbled upon this enormous, unprotected digital archive.
What made the discovery particularly alarming wasn’t just the volume of data, but its dynamic nature. During the month it took to identify and contact the hosting provider responsible (a global company relying on independent regional entities, in this case a Canadian subsidiary), Fowler observed the database grow in real time.
While attempting to have the resource removed for Terms of Service violations, new access logs continued to accumulate, suggesting that the source of the data was still active and operational.
The analyst was not able to definitively identify the owners or operators of the server, but the very structure of the archive left little room for imagination: it was an automated system designed to catalog and index stolen information on an industrial scale.
The numbers of the breach: from Gmail to cryptocurrencies
Analyzing the contents of the database, the figures that emerged are impressive and outline a cross-cutting risk landscape.
The largest share of compromised data concerns Gmail accounts, with as many as 48 million credentials exposed. Following that, the archive contained about 17 million accesses for Facebook and 4 million for accounts Yahoo. The Microsoft ecosystem was not spared either, with 1.5 million logins for Outlook, as well as as Apple, which saw around 900,000 accounts at risk for iCloud.
Particularly worrying is the presence of sensitive financial data. Within lines of code, 420,000 logins for Binance were identified, one of the world’s largest cryptocurrency exchange platforms, along with numerous logins for online banking services and credit cards.
This detail turns what might seem like a simple privacy breach into a real and immediate danger to the victims’ digital assets.
Fowler described the finding as a “criminals’ dream list“, highlighting how the variety of data allowed targeting users on multiple fronts simultaneously.
The danger of infostealers
According to the analysis conducted by Fowler, it is highly unlikely that these data originated from a direct breach of Google’s, Facebook’s, or the other involved companies’ servers. All evidence instead suggests that the database is the result of a malware infostealer.
These malicious software infect users’ devices (computers and smartphones) and act quietly using techniques such as keylogging to record everything the victim types on the keyboard, then sending the information to a remote server.
The meticulous organization of the data supports this theory. Each record was classified with a unique identifier that did not repeat, a system that facilitated searching and extracting of specific information.
This structure suggests that the archive had been designed to be queried by clients of cybercrime, perhaps interested in purchasing specific subsets of data to carry out targeted fraud.
Allan Liska, an intelligence analyst at the security company Recorded Future, highlighted how infostealers have dramatically lowered the entry barrier for criminals: with an investment of just $200 or $300 per month, anyone can rent infrastructures capable of collecting hundreds of thousands of passwords.
From streaming to state secrets
The breadth of the database covered every aspect of digital life. In addition to emails and social networks, 3.4 million logins for Netflix, 780,000 for TikTok and 100,000 for OnlyFans were found, demonstrating that even entertainment can be a vector of attack.
Even more troubling is the presence of 1.4 million academic and institutional accounts (domains .edu) and a “ton” of logins for government systems in several countries.
Although the database has been removed and is no longer publicly accessible, the incident serves as a stern reminder. The data could have been copied before the server was shut down.
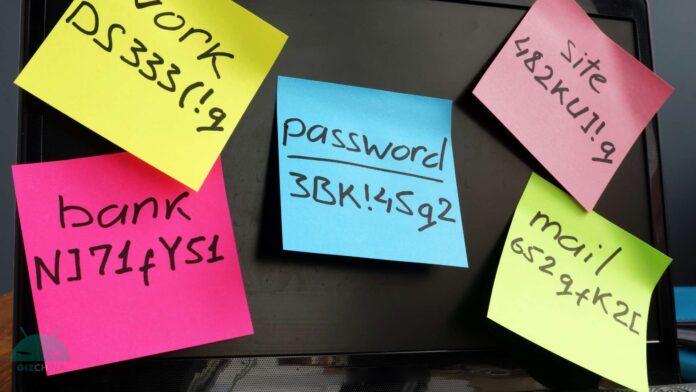
The recommendation is to immediately change the passwords for the mentioned services and, where possible, enable the two-factor authentication, the only real barrier against the use of stolen credentials.